Secure Development Lifecycle
June 19, 2020Security by Design
When thinking about (cyber)security, usally software tools like anti-virus, firewalls or a doorkeeper come to mind. When thinking about design, I see Italian cars and maybe furniture on my inner eye. Anti-virus is an endpoint-protection solution and ensures monitoring of malicious activity during operation of a host system. It is like a surveillance camera in front of a bank or somekind of fortress. I keeps the bad guys out or least detects them in daily business. Beeing the owner of some gold or physical asset in the bank just having a surveillance camera would not provide you enough trust in security of these – maybe in a car park. Some measures should already be made in before…
Fort Knox layered defense by design
A bank in extreme cases would be somewhat comparable to Fort Knox, as we know it from James Bond Goldfinger. With your grandmother’s jewellery at Kort Knox, would you have enough confidence in the security of these jewels? Am I correct?

And this is where “Security by Design” comes in. The terrain is intentionally built in such a way that many different obstacles and controls have to be overcome. From an outer fence (including surveillance cameras), to a grass field with guards and soldiers, to a strong building. Inside this building is a vault with additional gates (as far as James Bond Goldfinger is authentic). By the way, this is called “Defense-In-Depth”. A layered architecture of controls like an onion.
The CIA triade and security goals
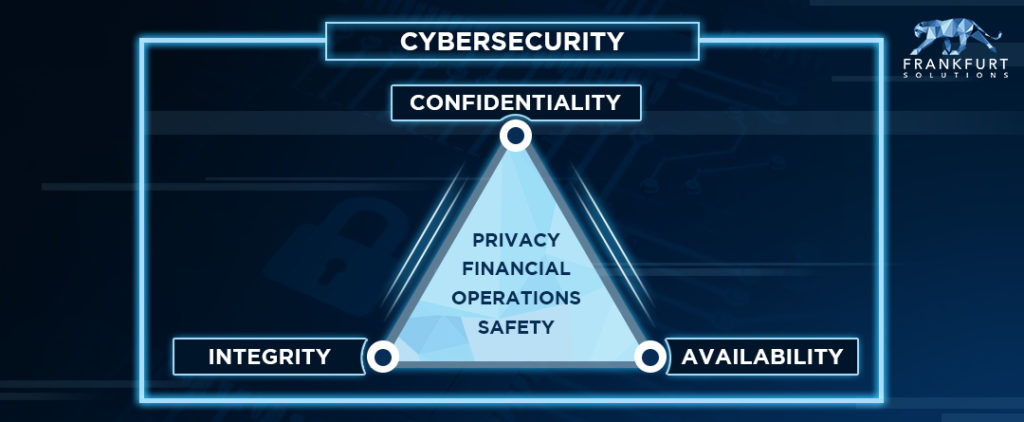
In information security, granny’s jewels are the organization’s data. Personally identifiable information such as your customers’ credit card numbers or perhaps sketches and requirement documents of your new product line. These should not be read by your competitors. In the Internet of Things and especially in Industry 4.0, integrity and availability are more important. Switching off the power grid or manipulating the voltage is not in the interest of our society or the operating utility company. There are more or less complex models to describe this. The most common and simplest is the CIA triad.
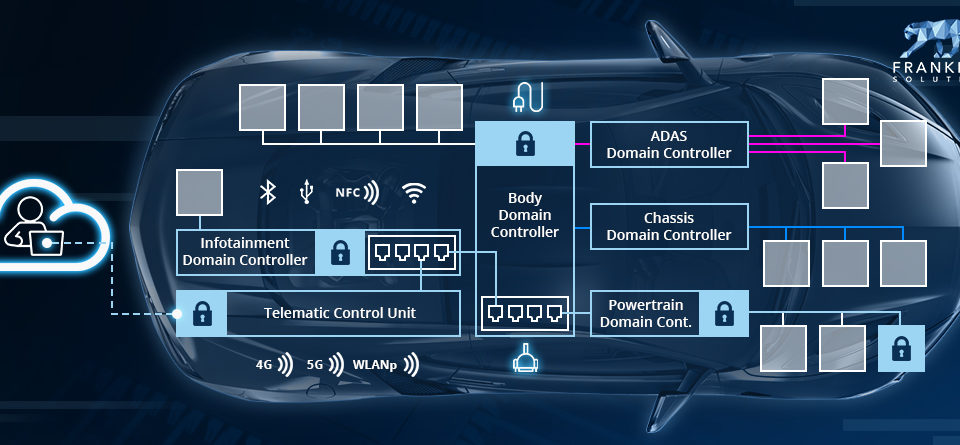
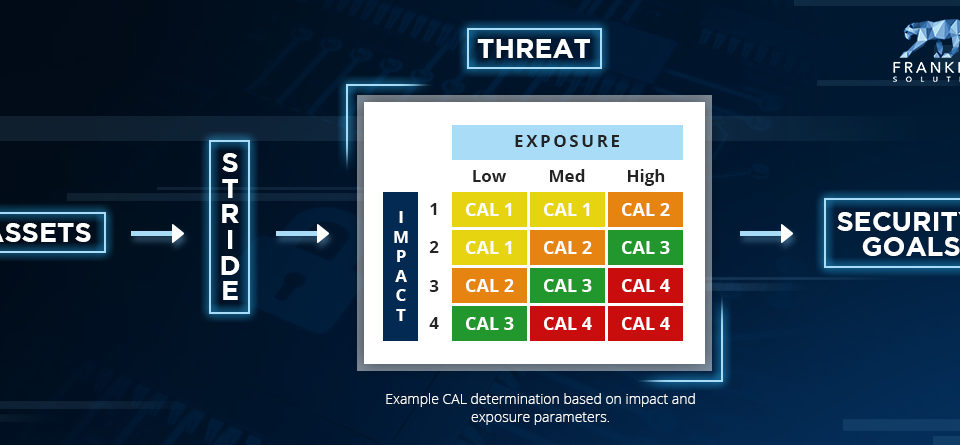
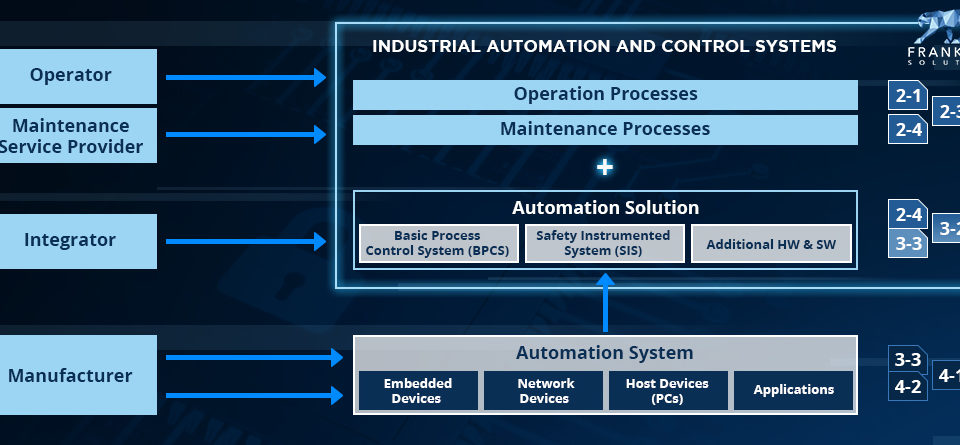
Threat modeling
Considering what you actually want to protect – these are your assets (be it your grandmother’s jewelry, your organization’s data, or the integrity of your oil production process), the way to define an secure architecture for your Fort Knox is to put yourself in the position of the intruder. This so-called threat modeling is an analytical brainstorming approach to defining your controls. These can be organizational – regularly check your surveillance cameras or security logs – or technical such as fences and firewalls. A good guide for conducting the analyses is to consider common attacks and vulnerabilities. You don’t have to reinvent the world. This also explains why medieval castles are not protected against aeroplanes – they simply didn’t exist at the time and therefore posed no threat to the castle owner or those responsible for determining the design. However, for proper implementation, one must combine cyber security background knowledge and detailed knowledge of the system in question.
The job is not done when you have created the plans of the castle. You still have to check if the fences and walls are built correctly. Then you should test them for weak points and instabilities and check regularly if new threats arise or your existing controls need to be updated. This is already a forecast for a complete Secure Development Lifecycle…
As you can imagine in the modern world, these current controls are implemented in hardware and software. However, in my point of view, the example of the fortress is beautiful and tangible and should be a good guide when designing a control unit or even a production facility.
—
I hope you enjoyed reading this article. If Security by Design is relevant for you in connection with IoT – for example in the development of automotive / industrial controls units or the planning of your production facility – please don’t hesitate to schedule an appointment or write my an E-Mail.
All the best, David!