Industrial Security – IEC 62443
July 8, 2020
Automotive Cybersecurity
July 17, 2020Threat Modeling & Risk Assessment
Connecting devices, cars, production lines, and even entire plants with cloud applications and complex networks offers tremendous opportunities and raises new cyber security challenges. Different technologies, protocols, threats and possible entry points for attackers via the Internet of Things do not make it easier. However, security is a must for safety-critical applications in the Industry 4.0 / IIoT such as power grids or connected vehicles.
So how can I secure any kind of system holistically?
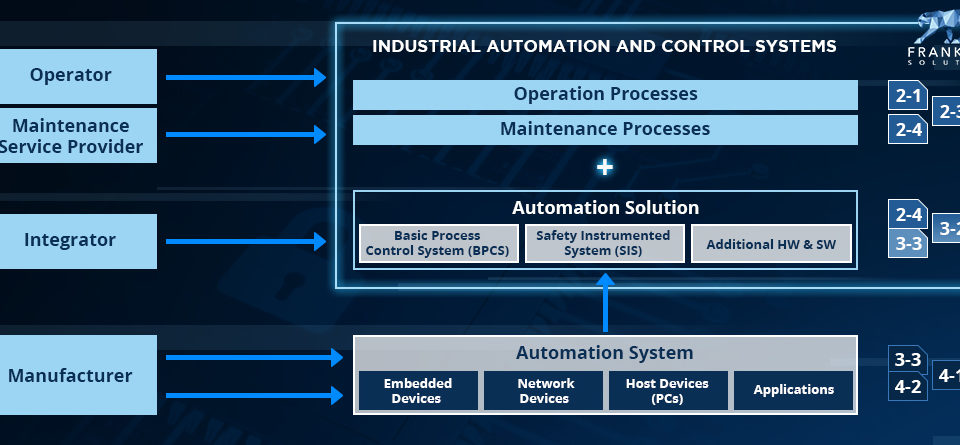
Just like a fragile wall or an open fence, the biggest holes should be closed first – in a risk-based approach. Fortunately, literature and standards such as IEC 62443-3-2 (especially for industrial plants) provide a methodology for risk assessment. As far as cars are concerned, the upcoming ISO/SAE 21434 “Road vehicles – Cybersecurity engineering” deals extensively with risk assessment and in particular threat modelling. The same applies to the secure development of industrial components or any other type of equipment described in the processes and tools of IEC 62443-4-1.
In completing the pyramid to the cloud, the Microsoft Secure Development Lifecycle (MSDL) and its international equivalent ISO 27034, which is dedicated to web security, do also take it into account. Threat modeling and overall risk assessment is the fundamental, most cost-effective, risk-based approach to secure everything from sensors to cloud applications. In the following, we’ll take a closer look at how it works.
What do I actually want to protect?
The first and most important question that is often asked after implementation and is sometimes not easy to answer is: What are the assets of the organisation I want to protect?
Traditionally and historically, in the world of information security and intelligence agencies is about sensitive data, and maintaining its confidentiality. It could be personally identifiable information (PII), such as credit card data in a cloud application or GPS data from a sensor that shows how a power plant is built when it is revealed. In the world of industrial processes, such a chemical process, business continuity, and the integrity of expensive machinery have a higher priority.
Ultimately, the owner of the equipment is responsible for data, systems and other things of overall value (including business processes such as a running web shop). However, it can be difficult to determine accountability between operators, system integrators and component manufacturers.
Another important aspect that often fails in project management is the definition of the scope or specifically the “system under consideration” (SUC). A great advantage of an analytical risk analysis is the possibility to zoom in and out. From a complete IIoT scenario to a single software component. Everything can be analysed and covered.
Beyond technology – a holistic picture
We have implemented state-of-the-art encryption and “our solutions are secure” are often used statements, which on the one hand are blindsighted and on the other hand do not cover the whole picture. The great advantage of threat modeling and risk assessment is the fact that it is an analytical approach, which in the best case uses comprehensive knowledge of cyber security and system experts. A vault is just as secure as the corresponding key or passcode. If encryption keys, source code or other design documents are published, even solid implementations become useless. In general, there are three types of security controls:
- Administrative – policies & procedures
- Logical (technical) – encryption, digital signatures, firewalls
- Physical – fences & guards
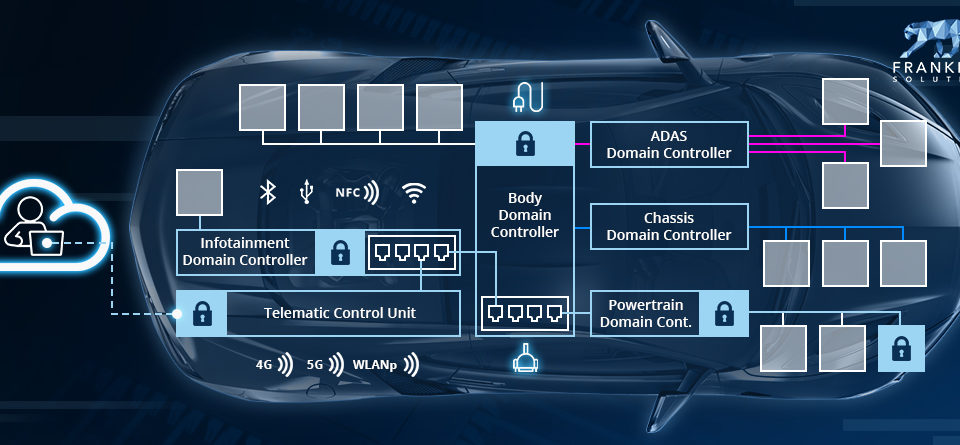
Effective protection is a combination of all these factors. A strong authentication policy without the enforcement of passwords (everyone uses 12345 or writes codes on the screen) is useless. The same applies if intruders gain physical access to the assets. For example, if a thief gets into a car and can access the OBD-II connector, most barriers are bypassed or ineffective. A simple rogue device can be used to start the engine and unlock the immobilizer.
An attacker centristic approach – think like the bad guys
Unlike in functional safety, risks cannot be determined in a statically measurable unit such as errors per hour. The adversary is not a mechanical problem or the susceptibility to failure of an electrical component, but an intelligent human being.
The basic idea of threat modelling is that the good guys find open holes or ask themselves how a system can be secure / insecure in a defensive approach before the bad guys do. Thinking like a hacker and finding a way in is a fundamentally different approach than what has been done before, especially in the area of industrial control systems.
At PenTest time it is already too late
White or ethical hackers take things apart in a reverse engineering approach. Details of the implemented design are identified, open vulnerabilities are uncovered and exploited. This approach prevents the bad guys from finding the open holes first and helps to identify implementation weaknesses or bugs and can also provide recommendations for design changes.
However, the “we already implemented the product and now we make sure it’s secure” approach leads to the use of band-aids and quick fixes. Only a security by design approach that considers the issue from the beginning of the development process will ensure that the vault is installed in the bank before the building is furnished.
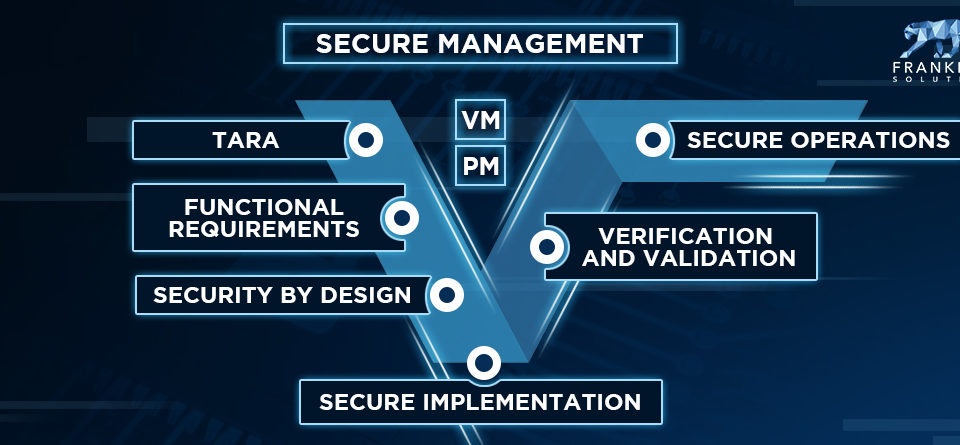
In the “Secure Development Lifecycle”, threat modelling and risk assessment is the first step and essential input for a functional concept and technical architecture. It can be carried out without existing technical implementations, while at the same time taking customer or market requirements into account. Penetration testing is at the end of the development lifecycle and represents a gateway to production and operation. Better than nothing, but as the only security consideration already too late.

Finding the priority – how risk is determined
A risk-oriented approach is in the best interests of the CFO and the controlling department. If security controls or other measures and not based on them, money simply it thrown in the wrong place. That makes them ineffective and costly. It also helps to lock systems appropriately and not beyond. If not done, the results are user complaints about spending too much time on two-factor authentication and beeing blocked from actual functionality and business process.
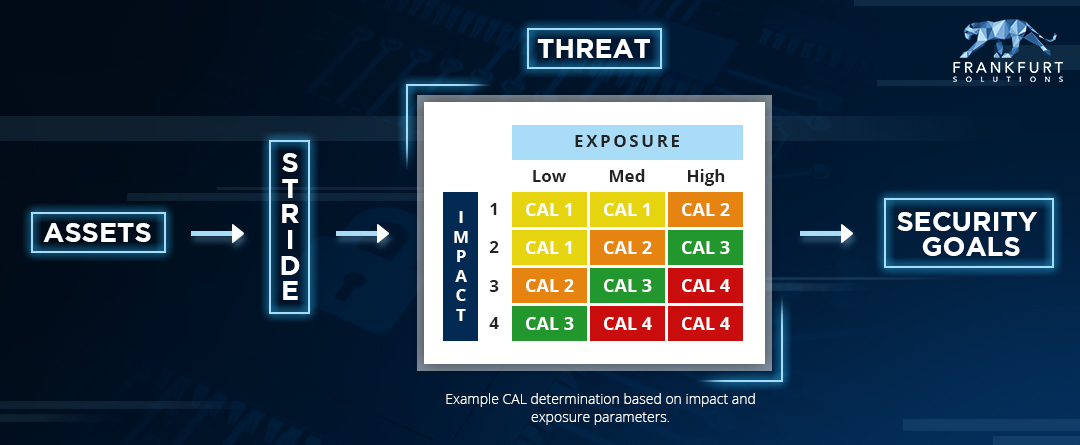
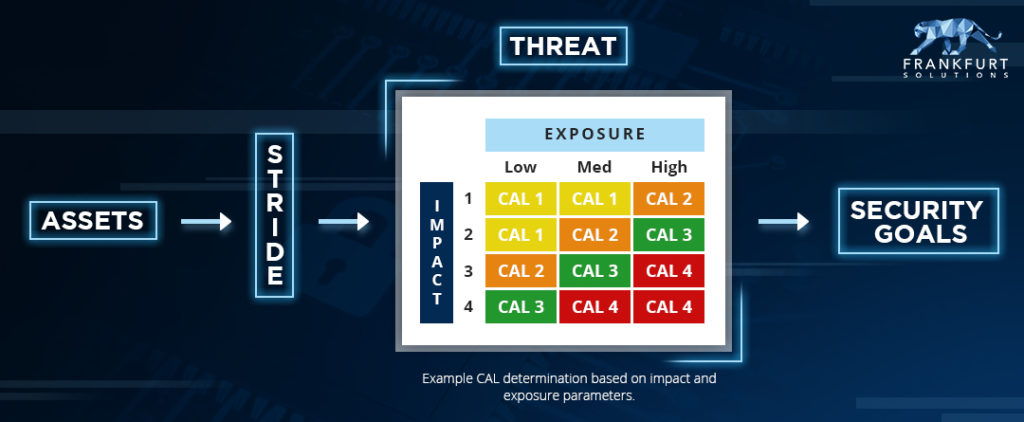
In connection to informatino security risk is determined in a matrix with two inputs:
- Attack surface / exposure / attack probability / likelihood
- Impact – environemental, financial, safety, operational consequences
An easily executed attack with catastrophic consequences means a high risk and must be tackled first. If an attack requires dedicated expertise and great effort, while the impact is mediocre, the need to act is less urgent.
Security Goals
If the risk was determined in a qualitative approach using cybersecurity knowledge and experts of the system under consideration, a priority list or, in agile language, “an ordered backlog” was created. The list of assets, a classification of threats and the level of risk determine the security goals. They are the basis for a functional security concept. Or in other words: “what do I need to do to mitigate these risks?” This in turn represents the next step in the development life cycle: The way I implement cyber security functionality in a defense-in-depth architecture.
—
I hope you enjoyed reading this article. If Threat Modeling & Risk Assessment is relevant for your organization – e.g. in connection with the coverage of mission critical IIoT / Industry 4.0 or connected car scenarios – please don’t hesitate to check out the corresponding training, schedule an appointment or write my an E-Mail..
All the best, David!