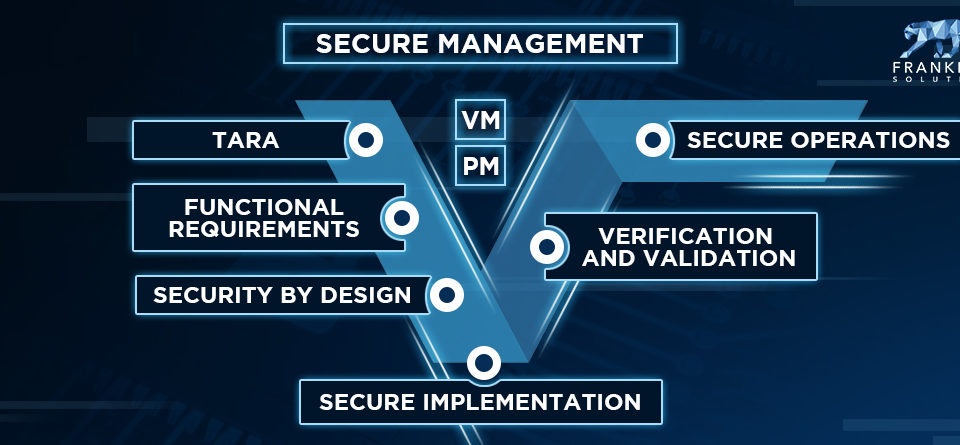
Secure Development Lifecycle
June 19, 2020
Threat Modeling & Risk Assessment
July 8, 2020Industrial Security – IEC 62443
Driven by industrial Internet of Things (IIoT) / Industry 4.0 applications, industrial networks and systems (Operational Technology – OT), which ran in an independent infrastructure (so-called airgapped), are connected to the IT and Cloud environment. The enormous overall benefits in terms of operational excellence and the possibility to develop new service models go hand in hand with increased connectivity and closing the gap between OT and IT. Unfortunately, this also increases the vulnerability for hackers to shut down, manipulate or spy on valuable and mission-critical industrial systems (just like an oil refinery).

So how can you secure industrial systems?
IEC 62443 is the most widely used standard for the protection of industrial automation and control systems. It is a series of documents divided into five sections:
- General
- Policies & Procedures
- System
- Component
Terms and metrics defined in “General” and help to understand the topic and find a common language. However, the focus of this article is to explain the basic principles of industrial asset protection in the following way:
- Risk based
- Across the supply chain
- Effective interation of process and systems
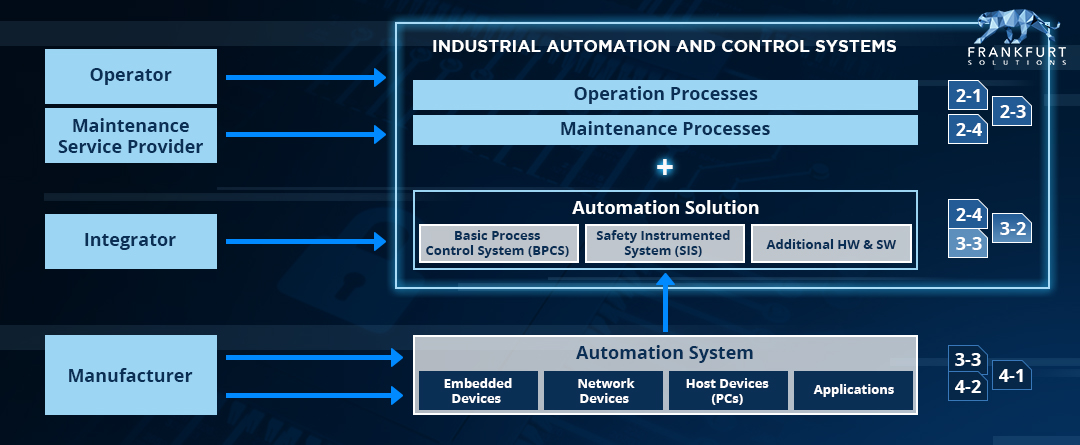
The most relevant documents and the overall structure is shown in the following figure:
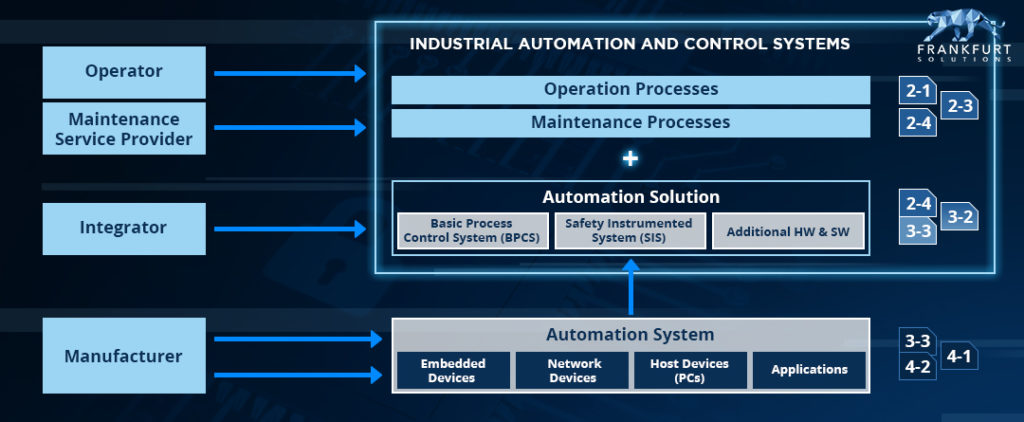
The operator, integrator and manufacturer
Ultimately, industrial automation and control systems run in an operator’s plant. These can be critical infrastructures and essential assets for the economy and society, e.g. in the process industry (power plants or oil refineries) and also in production plants such as in the automotive or the food and beverage industry.
Protection can only be achieved if the risk is managed and taken into account throughout the entire supply chain. Systems need to be securely designed, integrated, configured and operated correctly according to risk tolerance and business requiremetns. Operational processes are covered by 2-1, which is congruent with the information security mangement system according to ISO 27001. It deals, for example, with the correct use of passwords and accounts and ensures the monitoring of threats and attacks. No difference to the classical IT world, so we don’t explain it here in detail.
Integration processes are specified in 2-4. This is especially important for system integrators of automation solutions such as production lines, but can also be used to track maintenance providers. An entanglement example is the correct configuration of user accounts or the correct setup of authentication mechanisms including strong, non-standard passwords.
The initial provision of functional controls such as authentication and access are covered by the secure development lifecycle according to 4-1. Manufacturers of embedded / networked devices and industrial control systems can achieve security by design by following the appropriate processes.
Maturity + Technical Security = Protection
Technical security controls provide the basic ability to be secure. There are four levels of security (0 is no security at all). From SL1 the ability to protect against inadvertent misuse to SL4 the ability to protect against nation-state attacks.
The capability becomes effective in combination with appropriate development, integrationand operational processes. From ML1 – ad hoc lived processes to ML4 – optimized and conventionally improved processes (compared to CMMI level 4 and level 5 is merged to ML4).
Target, Capable & Achieved – The Security Levels
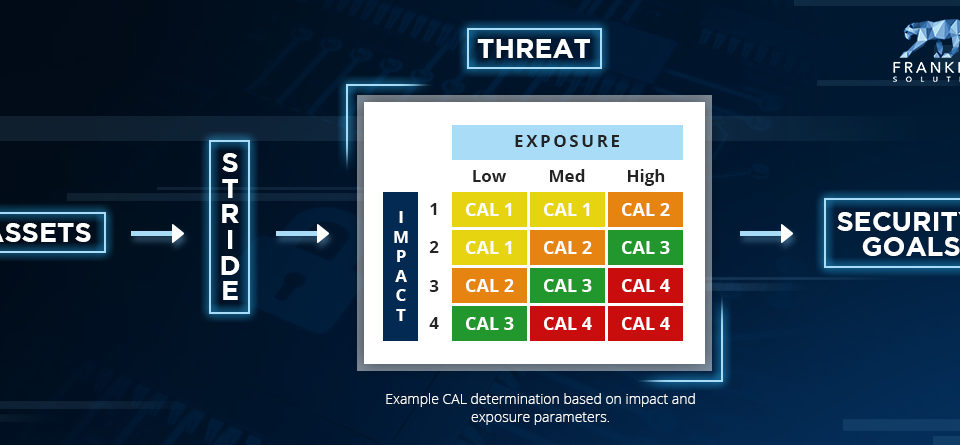
A risk-based approach, the reality of implementation and the trade-off between functionality and security are covered by differentiating security levels into the following areas:
- SL-T: The target security level provided by the operator of the facilities
- SL-C: The capable security level – the potential security by design that a component or system can achieve
- SL-A: The actually achieved security level in the operating environment
Industrial systems with a high capable level of security are expensive. As has already been mentioned, these investments must not be wasted, and it is therefore necessary to ensure and constantly evaluate their real effectiveness in the operational field.
Zones and conduits – Target security level
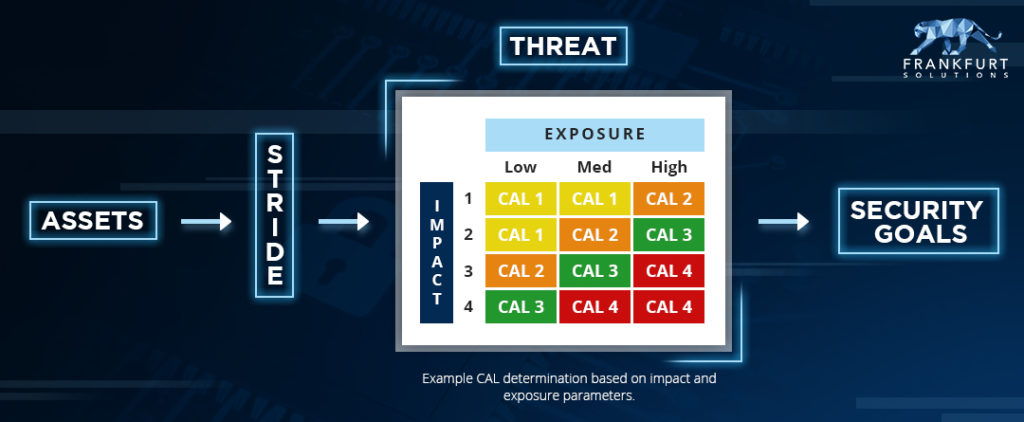
How is the target security level then determined?
It is specified by the facility operator after a proper risk assessment. The system under consideration (SUC) is based on the probability and impact of threats divided into zones and conduits with similar security requirements. The aim of defining target security and countermeasures is to reduce the risk until it matches the risk appetite of the organization. And no more – because this is costly and hinders functionality of value providing businss processes.
—
I hope you enjoyed reading this article. If Industrial Security is relevant for your organization – in connection with for example mission critial Industrial IoT and thus the development, integration and operation of industrial automation and controls systems – please don’t hesitate to check out the corresponding training, schedule an appointment or write my an E-Mail.
All the best, David!